Are you plan to implement a new security device as a security precaution you have implemented .Are you concerned that the IRS will reveal the personal information you provided while paying your taxes online, or that the DMV will reveal all of your personal information? That is not paranoia; it is logic. High-level breaches can and do occur, and there is little you can do about it. Other threats to your online security and privacy, on the other hand, are far closer to home. When you get down to write your manuscript one day, you may discover that all of the existing chapters have been encrypted by ransomware. You may also connect into your online banking system and find a big fat zero balance because a data-stealing Trojan has stolen your credentials. On the plus side, you can construct your own defense against these neighborhood issues.
You plan to implement a new security device Making your gadgets, online identity, and activities more simple secure requires very little work. In fact, several of our suggestions on how to be more simple secure online boil down to nothing more than common sense. These methods for improving your online security will keep you safer.
1. Install an anti-virus program and keep it up to date.
This type of software is known as antivirus software, but defending against actual computer viruses is only a minor fraction of what it does. Ransomware encrypts your files and demands payment in order to decrypt them.
Trojan horse applications appear to be legitimate apps, but they steal your personal information behind the scenes. Bots transform your computer into a zombie army soldier, ready to launch a denial-of-service attack, send spam, or do whatever the bot herder instructs. An excellent antivirus program will protect you from these and many other types of infection.
2. Investigate the Security Tools You Have Installed
Many wonderful apps and settings aid in the protection of your devices and identity, but they are only useful if you know how to use them correctly. To get the most out of these tools, you must first understand their features and settings. For example, your smartphone very definitely has a feature that allows you to locate it if it is misplaced, and you may have even activated it. But did you actively test it out so you’d know how to use it if it came in handy?
Most antivirus software can detect and block Potentially Unwanted Applications (PUAs), which are bothersome apps that aren’t malicious but don’t perform anything useful. However, not all of them make PUA detection the default setting. Check your detection settings to ensure they are set to block these annoyances. Similarly, your online security suite may contain components that are inactive until you activate them. When you install a new online security program, go through all of the primary window pages and at least look at the options.
To ensure that your antivirus is properly configured and functioning, visit the AMTSO website and use the online security features check page (Anti-Malware Testing Standards Organization). If your antivirus does not pass, contact tech support to find out why.

3. Use Different Passwords for Each Login
Getting a batch of login and password combinations from one source and trying those same combinations elsewhere is one of the simplest ways for hackers to obtain information. Assume hackers get your username and password by hacking an email provider. They may attempt to log in to banking websites or large online retailers using the same login and password combination. The single most effective approach to avoid a single data leak from causing a chain reaction is to use a strong, unique password for each and every online account you have.
Creating a unique and strong password for each account is an impossible task for a human. That is why you employ a password manager. Several excellent password managers are available for free, and it takes little effort to get started with one. Password managers that charge a fee, on the other hand, typically provide more functionality.
The only password you need to remember when using a password management is the master password that unlocks the password manager itself. When you unlock the password manager, it instantly logs you into your online accounts. This not only keeps you safer, but it also boosts your efficiency and production. You don’t have to waste time inputting logins or dealing with the time-consuming aggravation of resetting a forgotten password.
4. Obtain and Use a VPN
When connecting to the Internet over a public Wi-Fi network, you should use a virtual private network, or VPN.
Assume you go to a coffee shop and join a free Wi-Fi network. You have no idea about the online security of such link.
Someone else on that network could start searching through or stealing the files and data delivered from your laptop or mobile device without your knowledge. The owner of the hotspot could be a thief, sniffing out secrets from all Wi-Fi connections. A VPN encrypts your internet traffic and routes it through a VPN company-owned server. That implies that no one, not even the owner of the free Wi-Fi network, has access to your data.
Using a VPN conceals your IP address as well. Advertisers and trackers using that IP address to identify or geolocate you will instead see the VPN company’s address. Spoofing your location with a VPN server in another nation can also help you access content that isn’t available in your own country. On a more serious note, journalists and activists in oppressive nations have long utilized VPN technology to safely communicate.
The bottom line is that if you connect over Wi-Fi, whether on a laptop, phone, or tablet, you should use a VPN. If you’ve never used one before, or if the technology sounds a little out of your league, don’t worry; we’ve got you covered with this guide on how to set up and use a VPN.
5. Implement Two-Factor Authentication
Two-factor authentication is inconvenient, but it significantly increases the security of your accounts. To gain access to your accounts, you must first pass another layer of authentication, in addition to your login and password. If the data or personal information in an account is important or valuable, you should setup two-factor authentication if the account supports it. Gmail, Evernote, and Dropbox are just a few of the online applications that support two-factor authentication.
Two-factor authentication confirms your identity by requiring at least two separate sources of identification: something you are, something you have, or something you know. Naturally, the password is something you know.
Something you are could imply fingerprint or face recognition identification. Your cell phone could be an example of something you have. You may be asked to enter a text-messaged code or to hit a confirmation button on a mobile app. Something you have may potentially be a physical Security Key; Google and Microsoft have both shown a preference for this type of authentication.
If you only use a password for authentication, anyone who discovers it owns your account When two-factor authentication is activated, the password is rendered ineffective. Most password managers allow two-factor authentication, while some only demand it when a connection from a new device is detected. It is critical to enable two-factor authentication for your password management.
You can get started with our section on who has two-factor authentication and how to set it up.
6. Make use of passcodes even if they are optional.
Use a passcode lock wherever possible, even if it is optional. Consider all of the personal information and connections on your smartphone. It is unimaginable to go without a passcode lock.
Many cellphones come standard with a four-digit PIN. Don’t be satisfied with that. When biometric authentication is available, use it, and set a strong passcode rather than a silly four-digit PIN. Remember that even if you utilize Touch ID or something similar, you may still authenticate using the passcode, therefore it must be strong.
Ignore the six-digit option on modern iOS devices. Change Passcode (or Add Passcode if you don’t have one) by going to Settings > Touch ID & Passcode. If necessary, enter your old passcode. Choose Custom Alphanumeric Code on the screen where you’ll enter the new code. Enter a strong password, then save it in your password manager as a protected note.
Different Android smartphones provide different methods for establishing a strong passcode. Locate your device’s Screen Lock settings, enter your old PIN, then select Password (if available). Add a strong password and save it as a protected note, just like you did with the iOS device.
7. Use Your Smartphone to Pay
The credit card system is out of date and not particularly simple secure. That is not your fault, but you can do something about it. Instead of pulling out your credit card, use Apple Pay or an Android counterpart wherever possible. When it comes to apps, there are numerous options. In fact, we have a whole list of mobile payment apps.
Typically, setting up your smartphone as a payment device is an easy process. It normally begins with taking a photo of the credit card you’ll be using to back up your app-based payments. And that’s pretty much the end of the setup; you’re ready.

Point-of-sale terminals that accept smartphone payments typically display an icon, which can range from a picture of a hand holding a smartphone to a stylised representation of a radio wave. Simply set your device on the terminal, authenticate it with your thumbprint, and you’re done.
What makes that any better than using the credit card? The app creates a one-time authentication code that is valid only for the current transaction. Even if someone stole that code, it would be useless to them. Furthermore, using a smartphone app to pay avoids the danger of data theft by a credit card skimmer.
Some smartphone payment apps allow you to pay online using a one-time code similar to this. If yours does not, contact your credit card company. Typically, you are given a temporary credit card number to use in place of your actual credit card, and the costs are credited to your regular account. After the temporary card number expires, it will no longer be valid. When your credit card provider or bank calls to try to sell you an upgrade, inquire about one-time use card numbers.
You can also utilize third-party programs to simple secure one-time credit card numbers. Credit card numbers, email addresses, and phone numbers, for example, can be hidden using Abine Blur Premium. You continue to shop and chat as usual, but the merchant does not obtain your personal information.
8. Use distinct email addresses for various types of accounts.
People who are both extremely organized and rigorous about their online security frequently use various email addresses for different purposes in order to keep their online identities separate. If a phishing email purporting to be from your bank arrives at the account you solely use for social media, you know it’s a forgery.
Consider keeping a separate email address for signing up for programs that you wish to explore but may have questionable online security or may spam you with promotional messages. After you’ve thoroughly researched a service or app, sign up with one of your primary email addresses. Close the dedicated account and create a new one if it begins to get spam. This is a do-it-yourself version of the masked emails that Abine Blur and other throwaway email account services provide.
Many websites associate your email address with your username, but some allow you to use your own. Consider using a different username each time—after all, your password manager will remember it! Anyone attempting to access your account must now guess both the username and the password.
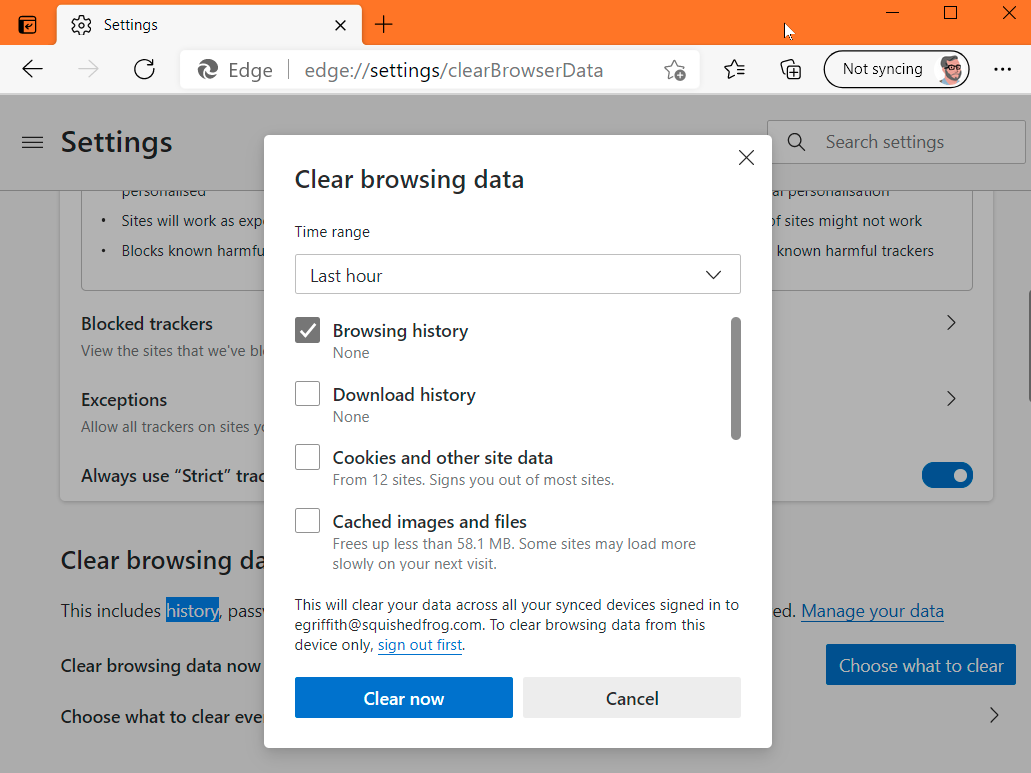
9. Clear Your Cache
Never underestimate the amount of information your browser’s cache has on you. Cookies, stored searches, and Web history could all link to a person’s home address, family details, and other sensitive information.
To better protect the information that may be lying in your browser history, erase browser cookies and clear your browser history on a regular basis. It’s simple. Simply press Ctrl+Shift+Del in Chrome, Edge, Firefox, Internet Explorer, or Opera to bring up a box that allows you to select which pieces of browser data to remove.
Some websites may be harmed if you delete cookies—you may lose whatever personalization you’ve applied.
Most browsers allow you to create a list of preferred websites whose cookies should not be deleted.
You may read our piece on how to clean your cache in any browser for a thorough guide on getting started.
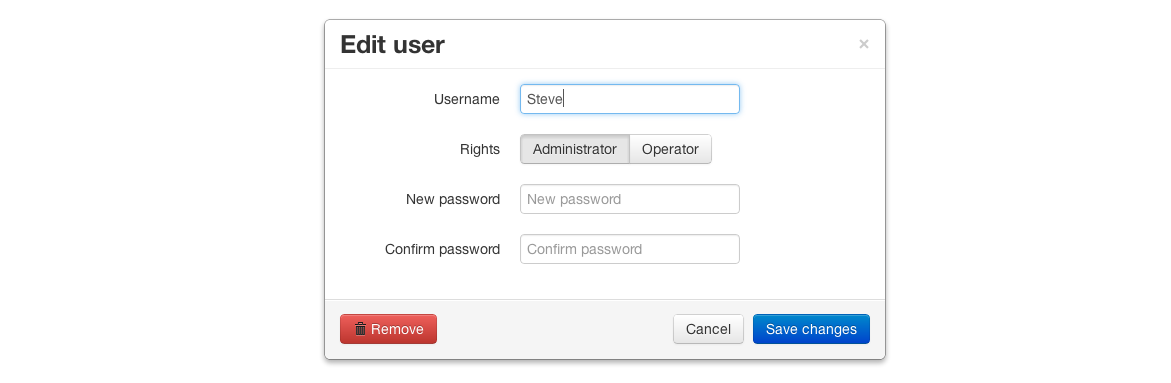
10. Disable the ‘Save Password’ function in browsers.
When it comes to what your browser knows about you, most browsers have a built-in password management solution. However, we at PCMag do not suggest them. We believe it is better to leave password protection to the professionals who create password managers.
Consider this. When you install a third-party password manager, it will usually offer to import your password from the browser’s cache. If the password manager can accomplish that, you can bet malicious software can as well.
Furthermore, storing your credentials in a centralized password manager allows you to use them across all browsers and devices.