The moment the internet became widely available, we all had endless opportunities for communication, information, learning, entertainment. Lately, we have been relying on the internet for more and more things. We need to learn about the basics of working on the Internet, to find out what actions can put us in an unwanted situation. We need to know what the potential consequences of our online activities are. Some of ours or the activities of others on the Internet may endanger our security. On the Internet, our privacy and reputation can be compromised, our money robbed in bank accounts, our computer disabled. Even personal and family safety can be compromised if we act carelessly online. The computer we use for surfing and related activities must have a program in place to identify and destroy hazards that could harm our computer and the data on it. There are sites and content on the internet where we can easily infect our computer, but also be embarrassed or fooled.
Regardless of all types of technical protection, we will never be fully protected and much depends on our click. What we all need to know and accept is that most abuse happens precisely through our inadvertently induced curiosity and ignorance. Today, it is unthinkable for many people to go through a single day without using the internet. However, some are not interested in the security field because they think their data is not important at all and that no one will try to compromise their privacy in any way. They forget that they are endangering themselves and others because their computers can easily be used as an indirect means of attacking other computers.
It is always a good time to take a few minutes to see if you are safe while online. The internet offers a lot of interesting content, but it also has its darker side. Anything that is not sufficiently protected is easily targeted by hackers. Even some seemingly harmless things, such as your date of birth, can be very useful for hackers, both amateurs and professionals alike, in combination with other information about you. News of how email accounts or social media accounts have been hacked often appears on the internet. Because we often open accounts on several social networks and email services, the question is whether our data is secure. Most ordinary internet users use passwords that they have never changed, or have done so before who knows how much time. Any code that does not change frequently can usually be easily detected by a simple trial and error method. In order not to put yourself in this situation, we advise you to change your old codes often (say, once or twice a month). Make sure that you do not select an easy-to-find or already-used code. There is a program that is efficient in using passwords and there is no need to remember them and is called a password manager.
If you change your password, do not use a password you have already used in the past. Do not use the same password in multiple different places. Do not use the “Remember password” option on applications such as a web browser. Do not write down your passwords in the form of text, e.g. in a word document or on paper. Make sure no one is watching the password you type password wallet. Certain services offer additional protection, such as security questions about some general information about you, such as “What is your place of birth?”.
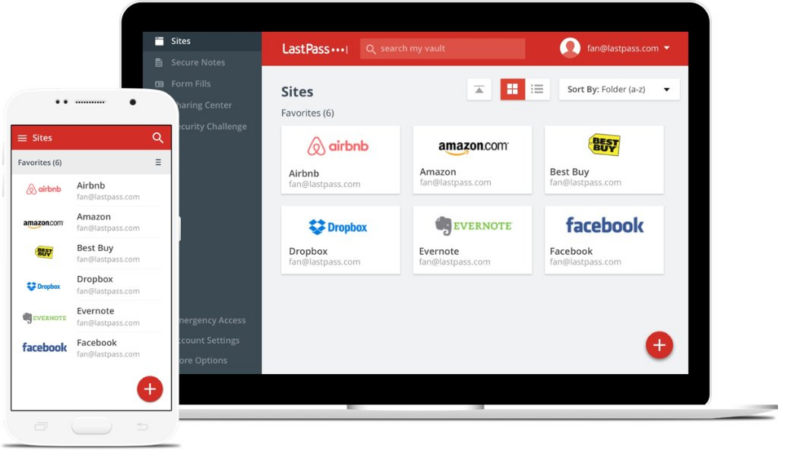
With a password manager, all you have to do is remember one strong password. Once your account is unlocked, you have access to all the other passwords you have stored within your account, making it easy to access all your other locations, services and devices. There are three basic types of password managers – password management software, password management services, and password management applications.
Each type of password manager has its own set of pros and cons, so your first step in choosing individual passwords or service software is to find out which type best suits your needs. The password manager that is one of the most common in use is Keeper Password Manager & Digital Vault. This particular password manager provides you with dark web protection, encrypted chat services and cloud-based vault for your passwords. It also comes as a browser extension, mobile app, desktop and web app and much more. Find out even further by reading this comprehensive review. When you need one of your passwords you just need to enter your master password in the password manager to unlock the database. The password manager will automatically retrieve the correct password and log you securely into the desired Password Managers website. This means that you do not have to remember your password protector or enter the access credentials manually.
Besides, most password managers also can synchronize automatically across multiple devices. Therefore, when you update your device manager password, these changes will be reflected in all your other devices. Finally, most password managers recognize when you create a new account and automatically update the database for you.
Of paramount importance is the master or master password you use to protect your password manager, and it should be unique and long. If your password manager supports two-factor authentication, be sure to use it ios password manager.

LastPass: The Most Expensive Password Manager
- Provides a free version
- Beyond free, the base fee is $36 per year.
- Windows, macOS, Linux, Android, iPhone, and iPad are all supported.
- Safari, Internet Explorer, Chrome, Firefox, Edge, and Opera browser extensions
LastPass’s free version formerly distinguished itself as the best password manager in this category by allowing you to save passwords, user login information, and credentials and sync them anywhere you want across mobile devices and browsers.
And while you can now monitor and manage passwords across mobile and desktop devices, as of late March, you’ll have to pick whether to utilize the free version for mobile or desktop.
That means that if you pick mobile, you’ll be able to access your LastPass account on your phones, tablets, and smartwatches, but not on your laptop or desktop software until you upgrade to Premium, which costs $36 per year, or Families, which costs $48 per year.
The best Premium version of the password manager also lets you share passwords, logins, memberships, and other stuff with authorized family and friends, use YubiKey for multifactor authentication, and receive 1 GB of protected storage.
Meanwhile, password manager app reviews the Families plan supplies you with six individual accounts, shared folders, and a dashboard for managing the family accounts and monitoring the security of your account.
Dashlane
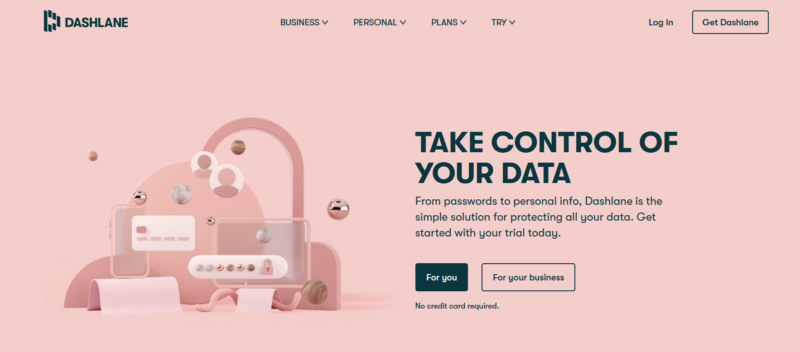
- Provides a restricted free version (50 passwords on one device)
- Beyond free, the starting price is $59.99 per year.
- Windows, MacOS, Android, iPhone, and iPad are all supported.
- Firefox, Safari, Internet Explorer, Edge, Chrome, and Opera browser extensions
Dashlane is a secure and straightforward solution to manage passwords and save other login information. We fun it as much as our other selections for password management. However, the free Dashlane app limits you to one device and 50 passwords.
- The $60 Premium membership is comparable to 1Password and LastPass.
- The $90 Family membership allows you access to six individual accounts.
1Password:
- 1Password: The most effective premium password manager for various platforms.
- Provides a trial version
- The base price is $35.88 per year.
- Linux, Chrome OS, Android, Windows, MacOS, iPhone, and iPad are all supported.
- Chrome, Firefox, Safari, Edge, and Opera browser extensions
1password password manager Suppose you need a reliable password manager tool to keep your login information private and secure. In that case, 1Password is the best password manager for the job, allowing you to access all of your accounts and services with a single master password protection services.
It is compatible with all major device platforms. This well-designed password manager does not have a free version, but you may check it out for 14 days before committing.
(Unfortunately, this is a reduction from the previous 30-day trial duration.)
Individual subscriptions cost $36 per year and include 1GB of document storage and optional two-factor authentication using Yubikey for further protection passwords tool.
A trip mode permits you to remove your 1Password exposed data from your device while traveling and then restore it with one click, making it impervious to border inspections easiest to use password manager.
Keeper
- Provides a restricted free version (unlimited passwords on one device)
- Beyond free, the starting price is $35.
- Windows, MacOS, Linux, Android, iPhone, and iPad are all supported.
- Internet Explorer, Chrome, Firefox, Safari, Edge, and Opera browser extensions
Keeper is yet another secure password manager software that allows you to manage login information on MacOS, Android, Windows, and iOS devices secure ways to store passwords.
A online password keeper free best version allows you to save an infinite password of passwords on a single device. The upgraded version costs $35 a year and allows you to sync passwords across numerous devices. You may also buy 10GB of secure file storage and dark web surveillance for roughly $59 per year multi user password manager.
It is entirely free; password keeper online however, donations are appreciated. Chrome OS, Android, Windows, MacOS, Linux, iPhone and iPad, BlackBerry, Windows Phone, and Palm OS are all supported. Web access, google password and common browser extensions, are available.
KeePassXC
(KeePassxc on other platforms, except the official Windows version, are unofficial ports.) Another open-source software password manager, KeePassxc began on Windows and has now been adapted to various platforms, including MacOS, Android, and iOS, utilizing the same code base how to securely store passwords.
On the bright side, it’s completely free and has the support of the Electronic Frontier Foundation. On the other hand, it’s only for sophisticated users: its user interface requires configuring to make all of the separately developed versions of KeePass function together. KeePass may be found here.
Bitwarden: The Most Effective Free Password Manager
- Secure, open-source, and transparent
- The free version can be used on an unlimited number of devices.
- Premium memberships begin at $10 per year.
- Windows, macOS, Linux, Android, iPhone, and iPad are all supported.
- Chrome, Firefox, Safari, Edge, Opera, Vivaldi, Brave, and Tor browser extensions
Bitwarden tops the list of the top best password managers for 2022 due to its open-source heritage and its unrivaled – and unlimited – free version. With comparative security strength, this very lightweight encryption program can generate, store, and automatically fill your passwords across all of your devices and big browsers, including Brave and Tor.
Its Password Managers free version lacks some of our other options’ bells and whistles, but its premium editions are feature-rich.
A Bitwarden premium subscription, like its rivals, lets you share passwords, logins, memberships, and other stuff with trusted family and friends, utilize multifactor authentication with YubiKey and get 1 gigabyte of encrypted storage. Despite having fewer capabilities than the premium version, Bitwarden’s free version has a one-to-one messaging tool called Bitwarden Send that allows you to share login credentials with another person securely.
Look no further if you’re searching for a user-friendly free password management service with a good security reputation.
Password managers are a great way to safely store all your passwords and other sensitive data and information. Their security is still up to you, and you must always use a unique and strong master password as well as the latest version of your chosen solution safest place to keep passwords.
How about NordPass or Norton Password Manager?
In the new months, top password managers there has been a movement in the VPN and antivirus software market. Many of the firms that created these software products extend them into larger software suites.
NordVPN, for example, now provides NordPass, a dedicated password manager, while Norton now includes a Norton Password Manager as part of its antivirus app and identity theft protection packages.
We haven’t exceptionally researched these password storage managers because they don’t currently appear to offer a feature set or pricing option that outperforms any of our top choices. If and when it changes, we’ll check into it further norton antivirus phone number.
No matter how much it looks like this, something involves people wanting what they create very weak orders before creating an account password. Never write down your passwords, especially not in places accessible to others. The password of any of your accounts should not be written on the screen. Never use passwords that are much more complicated and which you will forget. If it is necessary to write it down, do not specify for which account it is password and what is the account username. Paper on which it is recorded keeps away from the computer. There are no secrets on the internet and sometimes it’s better to keep something for yourself even from the best friends. No matter what your friendship is currently, anyone can always limit your password abuse. If you happen to write down your password somewhere, someone can easily get to it. So be careful not to get in trouble and keep your passwords for yourself! An important rule is to have different passwords at all orders and applications. In case of hacking, password and username can be shared public and accessible to anyone on the Internet. If you find it hard to remember so many different ones, password recommendation is to create groups. That’s right for social networks use one password, for The applications through which you communicate using a second password, for a school account, a third password.